I get a headache when I have to go over anything Anti-Virus but non the less I a have compiled a list of articles that covers a best/good practice when it comes to AV and Citrix. This list is not scientific but hopefully a start. I will include the links when I get more of a chance but I found some notes to myself and figured I would share.
Summary of recommended Citrix
· Scan on write events or only when files are modified. It should be noted that this configuration is typically regarded as a high security risk by most antivirus vendors. In high-security environments, organizations should consider scanning on both read and write events to protect against threats that target memory, such as Conficker variants.
· Scan local drives or disable network scanning. This assumes all remote locations, which might include file servers that host user profiles and redirected folders, are being monitored by antivirus and data integrity solutions.
· Exclude the pagefile(s) from being scanned.
· Exclude the Print Spooler directory from being scanned.
· Exclude specific files and folders within the \Program Files\Citrix directory that are accessed or modified frequently. For example, the Local Host Cache (imalhc.mdb) and Application Streaming offline database (RadeOffline.mdb) files may need to be excluded from the \Independent Management Architecture sub-directory. The local Resource Manager Summary Database file (RMLocalDatabase.mdb) may also need to be excluded from the \Citrix Resource Manager\LocalDB sub-directory. If Application Streaming is used, the \RadeCache and \Deploy folders may need to be excluded as well. While entire directories can be excluded, it should be noted that this is not considered a best practice by most antivirus vendors. In high-security environments, organizations should consider excluding specific files using exact names, such as ‘imalhc.mdb’. If exact file names cannot be used, Citrix recommends using wildcard exclusions to limit the attack surface area.
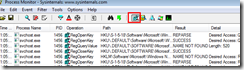
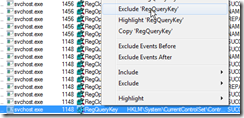
· Remove any unnecessary antivirus related entries from the Run key (HKLM\Software\Microsoft\Windows\Current Version\Run).
· If pass-through authentication is being used, for example, in a XenDesktop or Shared Hosted desktop scenario, exclude the XenApp Online Plug-in bitmap cache directory (typically %AppData%\ICAClient\Cache).
· If using the streamed user profile feature of Citrix Profile management, ensure the antivirus solution is configured to be aware of Hierarchical Storage Manager (HSM) drivers. For more information, refer to Profile Streaming and Enterprise Antivirus Products
Citrix Provisioning AV Best practices
· Limit antivirus definition updates to the Target Device. Create a plan to upgrade the vDisk periodically using manual, automatic, or automated techniques, such as Automatic vDisk updates or by using something like WorkFlow Studio.
· Avoid scanning the disk write cache location regardless of where this file resides. In limited testing, it is observed that most scanners cannot detect a virus within this location, because of their inherent design and the methods used to determine a virus.
· Avoid scanning the BNDevice.exe process on the Target Device. There are a few drivers that should be excluded from scanning in the <systemroot>\Windows\System32\Drivers folder such as:
o Provisioning Server 5.6 exclude BNNS.sys, BNNF.sys, BNPort.sys, bnistack.sys, and BNITDI.sys
o Provisioning Server 6.0 or later exclude bnistack6.sys,CvhdBusP6.sys, CFsDep2 .sys
· Avoid scanning the following processes on the Provisioning Server
o StreamService.exe
o StreamProcess.exe
o soapserver.exe
NDIS Filter Driver from Third Party Product on Target Device Interferes with Connection to Provisioning Services
The load order of the NDIS filter driver from third party product might interfere with the connection to Provisioning Services. The Start type of the driver must be 0x0(Boot) to utilize Provisioning Services properly. Otherwise, Provisioning Services driver cannot send and receive packets at the time of OS start.
Important! Citrix recommends you to consult the third party before trying the following solution.
Caution! Refer to the Disclaimer at the end of this article before using Registry Editor.
—
[HKEY_LOCAL_MACHINE\SYSTEM\CurrentControlSet\services\(driver name)]
"Type"=dword:00000001
"Start"=dword:00000000
"ErrorControl"=dword:00000001
"Tag"=dword:00000018
…
"Group"="NDIS"
"NdisMajorVersion"=dword:00000006
"NdisMinorVersion"=dword:00000000
—
Note: It is a necessary condition that Start type is set to 0x0(Boot). However, other factors in network driver of third party product could also cause an interference with Provisioning Services. See also CTX117395
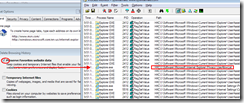
EdgeSight client AV Best practices
Complete the following procedure to configure your antivirus software (TrendMicro, Symantec, Norton, McAfee and so on.) to NOT scan the EdgeSight data folder or processes. This should be done on all of the devices that are or will be running the EdgeSight agent. You might need to contact your security administration team to put these exceptions in place enterprise wide.
Note: Citrix recommends that you follow this procedure before the deployment of any EdgeSight agents.Exclude the following agent folders from being scanned. Check a few agent devices to confirm the exact folder locations in your environment. These folders contain the EdgeSight agent database file and many log files. Following is the default installation location:
<AllUserProfile>\Application Data\Citrix\System Monitoring\Data
Exclude the following EdgeSight agent executables (processes) from being scanned. Listed below are the default installation locations:
<ProgramFiles>\Citrix\System Monitoring\Agent\Core\rscorsvc.exe
<ProgramFiles>\Citrix\System Monitoring\Agent\Core\Firebird\bin\fbserver.exe
Microsoft Recommendations (link below) AV Best Practices
Turn off scanning of Windows Update or Automatic Update related files
· Turn off scanning of the Windows Update or Automatic Update database file (Datastore.edb). This file is located in the following folder:
%windir%\SoftwareDistribution\Datastore
· Turn off scanning of the log files that are located in the following folder:
%windir%\SoftwareDistribution\Datastore\Logs
Specifically, exclude the following files: ◦ Res*.log
Edb*.jrs
Edb.chk
Tmp.edb
The wildcard character (*) indicates that there may be several files.
Turn off scanning of Windows Security files
Add the following files in the %windir%\Security\Database path of the exclusions list:
*.edb
*.sdb
*.log
*.chk
*.jrs
Note If these files are not excluded, antivirus software may prevent proper access to these files, and security databases can become corrupted. Scanning these files can prevent the files from being used or may prevent a security policy from being applied to the files. These files should not be scanned because antivirus software may not correctly treat them as proprietary database files.
Turn off scanning of Group Policy related files
Group Policy user registry information. These files are located in the following folder:
%allusersprofile%\
Specifically, exclude the following file:
NTUser.pol
Group Policy client settings file. This file is located in the following folder:
%Systemroot%\System32\GroupPolicy\
Specifically, exclude the following file:
Registry.pol
SEP Best practices on Terminal Servers
Symantec Endpoint Protection client will run acceptably on Windows Terminal Servers; however there are a few modifications than can be made in order to optimise the overall user experience.
AntiVirus and AntiSpyware protection
The following recommendations should be taken into account:
Configure Auto-Protect to:
· Scan when a file is modified
· Disable network scanning
Centralized Exceptions
It is recommended to:
· Exclude the pagefile
· Exclude the print spooler folder
· If the server is a license server, exclude the license server folder and databases
Some server administrators may wish to exclude their users roaming profiles and/or “My Documents” folders from being scanned for security risks. While this will improve performance, Symantec would not recommend this approach – in practice this is generally the location in which
security risks are discovered.
Scheduled Scans
If a scheduled scan is required then it should be run out of hours in order to minimise user impact. In addition, ActiveScans when new definitions arrive and startup scans should not be run as they could place unnecessary load on the terminal server during business hours.
Tamper Protection
There are no tamper protection recommendations for a server just running Terminal Services
Network Threat Protection
Although it is not recommended to run Network Threat Protection on terminal servers, it is entirely possible to do so. The default Symantec Endpoint Protection rule set will allow all terminal services functions to work correctly. However, it should be noted that if a custom rule set is
created, the following services and ports should be allowed:
In addition to the AntiVirus and AntiSpyware exclusions for standard terminal servers, the following exclusions are recommended for Citrix servers:
1. Citrix program files folder
2. Citrix configuration database if present on the server
It is recommended that the following process is excluded from Tamper Protection on Citrix servers, as it is known to cause problems:
· ctxcpusched.exe – for more details on this process and how to create an exclusion for it, please refer to Appendix E.
SEP in non persistent VDesktops
Using Symantec Endpoint Protection in non-persistent virtual desktop infrastructures
Set up the base image.
Step
Setting up the base image for non-persistent guest virtual machines in virtual desktop infrastructures
Description
Step 1
Install Symantec Endpoint Protection on the base image.
See About client deployment methods.
Step 2
In Symantec Endpoint Protection Manager, disable Tamper Protection so that you can modify the registry.
See Changing Tamper Protection settings.
TO change Tamper Protection settings
1. In the console, click Clients.
2. On the Policies tab, under Settings, click General Settings.
3. On the Tamper Protection tab, check or uncheck Protect Symantec security software from being tampered with or shut down.
4. In the list box under Actions to take if an application attempts to tamper with or shut down Symantec security software, select one of the following actions:
5. Log only
6. Block and do not log
7. Block and log
8. Click the icon to lock or unlock the options on client computers. When you lock an option, you prevent user changes to the option.
9. 6.Click OK.
Step 3
Create a registry key on the base image to mark the GVMs as non-persistent clients.
To create a registry key to mark the base image GVMs as non-persistent clients
1. After you have installed the Symantec Endpoint Protection client and disabled Tamper Protection, open the registry editor on the base image.
2. Navigate to HKEY_LOCAL_MACHINE\SOFTWARE\Symantec\Symantec Endpoint Protection\SMC\.
3. Create a new key named Virtualization.
4. Under Virtualization, create a key of type DWORD named IsNPVDIClient and set it to a value of 1.
Step 4
In Symantec Endpoint Protection Manager, enable Tamper Protection again.
See Changing Tamper Protection settings.
In Symantec Endpoint Protection Manager, configure a separate purge interval for offline non-persistent VDI clients.
See Configuring a separate purge interval for offline non-persistent VDI clients.
Configuring a separate purge interval for offline non-persistent VDI clients
To configure the purge interval for offline non-persistent VDI clients
1.In the Symantec Endpoint Protection Manager console, on the Admin page, click Domains.
2.In the Domains tree, click the desired domain.
3.Under Tasks, click Edit Domain Properties.
4.On the Edit Domain Properties > General tab, check the Delete non-persistent VDI clients that have not connected for specified time checkbox and change the days value to the desired number.
The Delete clients that have not connected for specified time option must be checked to access the option for offline non-persistent VDI clients.
5.Click OK.
Best practices for virtualization with Symantec Endpoint Protection 12.1, 12.1 RU1, and 12.1 RU1 MP1
http://www.symantec.com/business/support/index?page=content&id=TECH173650
Too many to list
Symantec Endpoint Protection 12.1 – Non-persistent Virtualization Best Practices
Client Recommendations
The following configuration recommendations will ensure that SEP client installations in non-persistent VDI environments do not generate network and disk IO from advanced SEP client features which they will not benefit from.
1.Make the following changes to the Communications Settings policy:
1.Configure clients to download policies and content in Pull mode
2.Disable the option to Learn applications that run on the client computers
3.Set the Heartbeat Interval to no less than one hour
4.Enable Download Randomization, set the Randomization window for 4 hours
Make the following changes to the Virus and Spyware Protection policy:
1.Disable all scheduled scans
2.Disable the option to "Allow startup scans to run when users log on" (This is disabled by default)
3.Disable the option to "Run an ActiveScan when new definitions Arrive"
3.Avoid using features like application learning which send information to the SEPM and rely on client state to optimize traffic flow
Image Maintenance
Add the following steps to the routine maintenance schedule for base images. Symantec recommends performing these maintenance tasks at least once a week.
1.Update all applicable definitions and security content on the base image with the latest content available
2.Confirm the SEP client on the base image is able to communicate with its SEPM server(s)
3.Confirm the SEP client is using the correct VDI-specific policies
Before redistributing the image:
1.Remove any temporary files associated with the SEP client, including
2.Remove hardware key information from the base image using How to prepare a Symantec Endpoint Protection 12.1 client for cloning
Follow the general best practices below for periodic image maintenance and testing.
1.Manually upgrade the SEP client on the base image rather than using auto-upgrade for the VM client policy groups
2.Test performance optimizations. For instance, reducing memory allocated to a VM can cause increased OS swapping and defeat hypervisor optimizations like memory page deduplication
3.To minimize the size of the base VM image, disable client install caching and set content cache revisions to 1. See http://www.symantec.com/business/support/index?page=content&id=TECH106042
4.Configure VM refreshes to occur on logoff. Set the pool of available VM’s large enough so that users can easily access a running image which was updated in the background
Symantec Endpoint Protection Manager settings
1.Configure SEPM to keep definitions at least as long as the minimum image refresh frequency. E.g. Keep 30 days if the maximum image age is 14 days
2.SEPM will ‘remember’ all new images attaching, which can build up quickly in a VDI environment. An admin can either reduce the interval required for clients to age out of SEPM or periodically run a cleanup script which purges the old client records.
Reference Articles
Citrix Guidelines for Antivirus Software Configuration
http://support.citrix.com/article/CTX127030
Provisioning Services Antivirus Best Practices
http://support.citrix.com/article/CTX124185
Required Antivirus Software Configuration for the EdgeSight Server
http://support.citrix.com/article/CTX114906
Virus scanning recommendations for Enterprise computers that are running currently supported versions of Windows
http://support.microsoft.com/kb/822158
NDIS Filter Driver from Third Party Product on Target Device Interferes with Connection to Provisioning Services
http://support.citrix.com/article/CTX137505
derived from this article
SEP Firewall does not function with Citrix’s Provisioning Server.
http://www.symantec.com/business/support/index?page=content&id=TECH205982
Here are the details about the new separate VDI purging interval:
http://www.symantec.com/business/support/index?page=content&id=HOWTO81133#v75342792 (step 2 has already been done in the manager)
Some documents on best practices (we’d have to chat about some of these… def updates are vitally important unfortunately, so updating only the base image won’t fly):
http://www.symantec.com/business/support/index?page=content&id=TECH173650 (virtualization in general)
http://www.symantec.com/business/support/index?page=content&id=TECH180229 (VDI non-persistent clients
Also
Issues with Citrix XenDesktop / PvD and Symantec Endpoint Protection 12.1
http://www.symantec.com/connect/forums/issues-xendesktop-pvd-and-symantec-endpoint-protection-121
leads to
Installing Symantec Endpoint protection on a VDI with Personal Vdisk